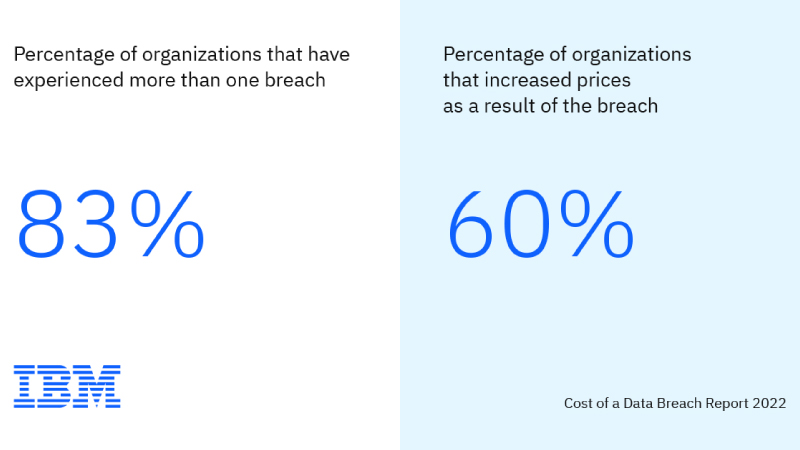
60 per cent of breached businesses raised product prices post-breach, the vast majority of critical infrastructure lagging in zero trust adoption
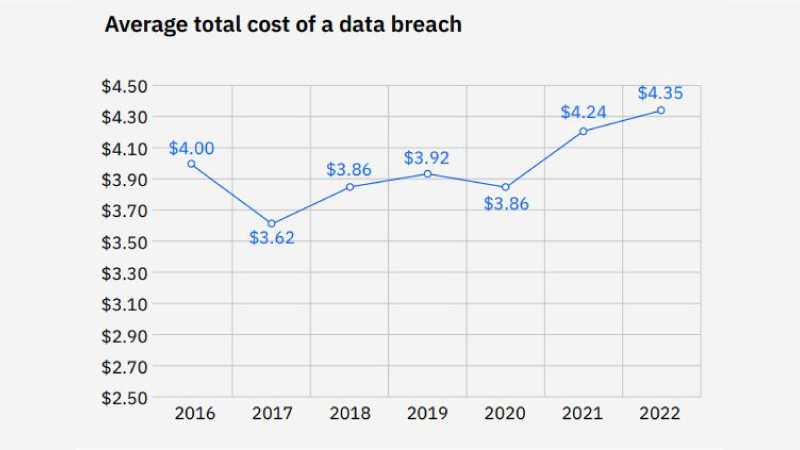
A recently released study, the Cost of a Data Breach Report by IBM Security revealed costlier and higher-impact data breaches than ever before, with the global average cost of a data breach reaching an all-time high of $4.35 million for studied organisations. The 2022 Cost of a Data Breach Report is based on an in-depth analysis of real-world data breaches experienced by 550 organisations worldwide between March 2021 and March 2022. The Ponemon Institute conducted the research, sponsored and analysed by IBM Security.
The cost of breaches has increased by over 13 per cent over the previous two years, and the data imply that these incidences may potentially be a factor in growing prices for products and services. The “haunting effect” that data breaches are having on businesses is made clear by the fact that 83 per cent of the analysed organisations had experienced more than one data breach in their lifespan and that over 50 per cent of breach expenses are spent more than a year after the breach.
“Businesses must put their security defences on the offence and beat attackers to the punch. It’s time to stop the adversary from achieving its objectives and start to minimise the impact of attacks. The more businesses try to perfect their perimeter instead of investing in detection and response; the more breaches can fuel the cost of living increases. This report shows that the right strategies coupled with the right technologies can help make all the difference when businesses are attacked,” said Charles Henderson, Global Head of IBM Security X-Force.
Some of the key findings in the 2022 IBM report include:
- Lack Of Zero Trust Infrastructure– Nearly 80 per cent of critical infrastructure organisations don’t use zero trust tactics, and as a result, average breach costs have increased to $5.4 million, or $1.17 million more than those who do. Ransomware or damaging assaults accounted for 28 per cent of breaches at these organisations.
- A High Price To Pay – Ransomware victims who opted to pay threat actors’ ransom demands saw only $610,000 less in average breach costs compared to those who chose not to pay – not including the cost of the ransom. Factoring in the high cost of ransom payments, the financial toll may rise even higher, suggesting that simply paying the ransom may not be an effective strategy.
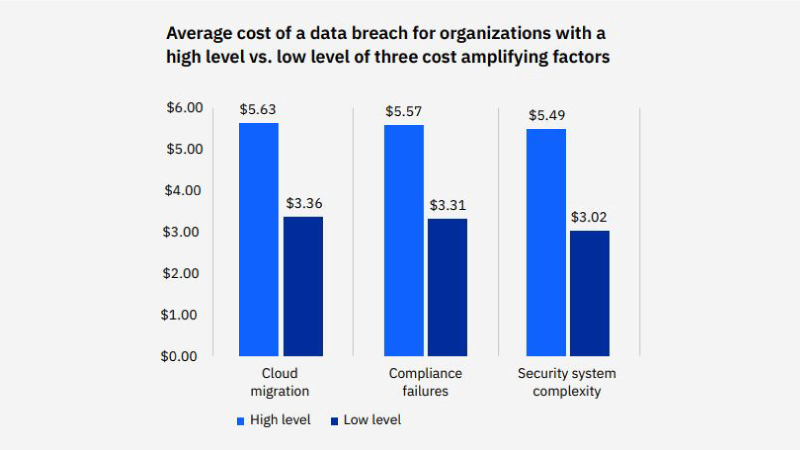
- Cloud Immaturity– Forty-three per cent of studied organisations are in the early stages or have not started applying security practices across their cloud environments, observing over $660,000 on average in higher breach costs than studied organisations with mature security across their cloud environments.
- Security AI and Automation Lead as Cost Savers – Participating organisations fully deploying security AI and automation incurred $3.05 million less on average in breach costs compared to studied organisations that have not deployed the technology – the most significant cost saver observed in the study.
Over-trusting Critical Infrastructure
Over the past year, there have been growing concerns about the targeting of key infrastructure throughout the world, and several governments’ cybersecurity authorities have urged citizens to remain vigilant against disruptive attacks. In fact, the study of critical infrastructure organisations found that ransomware and damaging assaults accounted for 28 per cent of breaches, demonstrating how threat actors are attempting to destabilise the international supply networks that depend on these organisations. This covers businesses in the healthcare, industrial, transportation, and financial services sectors. A mere 21 per cent of the critical infrastructure organisations use a zero trust security paradigm. Additionally, 17 per cent of breaches at critical infrastructure organisations resulted from the initial penetration of a business partner, demonstrating the security concerns that excessively trusting settings provide.
The High Cost Of Ransom
Businesses who complied with ransom requests from threat actors paid $610,000 less in average breach expenses than those not considering the ransom sum. However, when accounting for the average ransom payment, which according to Sophos reached $812,000 in 2021, businesses that opt to pay the ransom could net higher total costs – all while inadvertently funding future ransomware attacks with capital that could be allocated to remediation and recovery efforts and looking at potential federal offences. The persistence of ransomware, despite significant global efforts to impede it, is fueled by the industrialisation of cybercrime.
IBM Security X-Force discovered the duration of studied enterprise ransomware attacks shows a drop of 94 per cent over the past three years – from over two months to just under four days. These exponentially shorter attack lifecycles can prompt higher impact attacks, as cybersecurity incident responders are left with very short windows of opportunity to detect and contain attacks. With “time to ransom” dropping to a matter of hours, businesses must prioritise rigorous testing of incident response (IR) playbooks ahead of time. But the report states that as many as 37 per cent of organisations studied that have incident response plans don’t test them regularly.
Hybrid Cloud Advantage
Among the organisations investigated, hybrid cloud environments were the most common infrastructure (45 per cent) in use. Businesses using a hybrid cloud architecture had lower breach costs, averaging $3.8 million, than those using a strictly public or private cloud approach, which saw average breach costs of $5.02 million and $4.24 million, respectively. Adopters of hybrid clouds were able to find and stop data breaches 15 days more quickly on average than participants overall, who took 277 days.
The importance of cloud security is shown by the fact that 45 per cent of breaches happened in the cloud. However, despite greater breach costs, 43 per cent of organisations claimed they are only beginning to implement security policies to safeguard their cloud infrastructures. Businesses in the study that did not consistently deploy security measures across all domains took an average of 108 more days to detect and contain a data breach than those that did.
Additional findings in the 2022 IBM report include:
- Phishing Becomes Costliest Breach Cause – While compromised credentials continued to reign as the most common cause of a breach (19 per cent), phishing was the second (16 per cent) and the costliest cause, leading to $4.91 million in average breach costs for responding organisations.
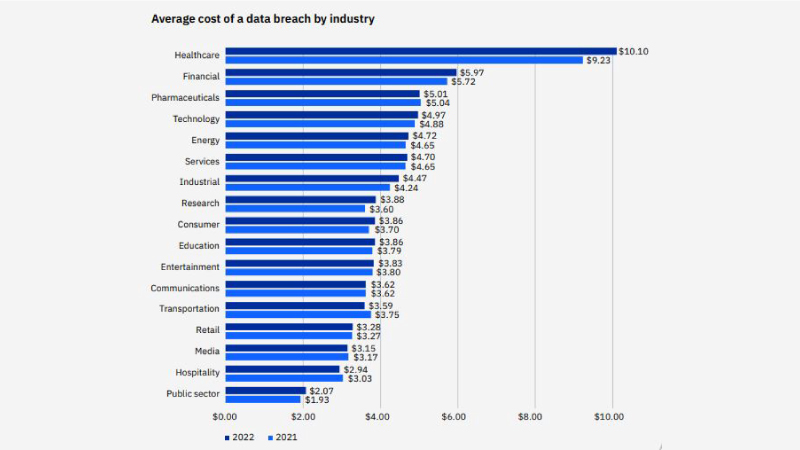
- Healthcare Breach Costs Hit Double Digits – For the 12th year in a row, healthcare participants saw the costliest breaches amongst industries, with average breach costs increasing by nearly $1 million to reach a record high of $10.1 million.
- Insufficient Security Staffing – Sixty-two per cent of studied organisations stated they are not sufficiently staffed to meet their security needs, averaging $550,000 more in breach costs than those that state they are adequately staffed.
If you liked reading this, you might like our other stories
One Year of GDPR: Privacy Laws, Data Breaches, and the Impact of Regulations
Data Privacy In Metaverse Is An Evolving Concern









