When organisations fail to keep up with the volume and variety of machine identities they need, the consequences can be dire
The number of machines enterprise security teams today work with and manage is burgeoning exponentially. In modern computing infrastructure, servers are replaced by virtual machines, which evolved into containers and are now adapted to serverless cloud functions. With the widespread IoT devices, Internet connectivity and processing capabilities have improved operating speed in relatively isolated machines. According to a Cisco report, there were 20 billion devices connected to the Internet in 2021, and the number is expected to jump to 29 billion by 2023.
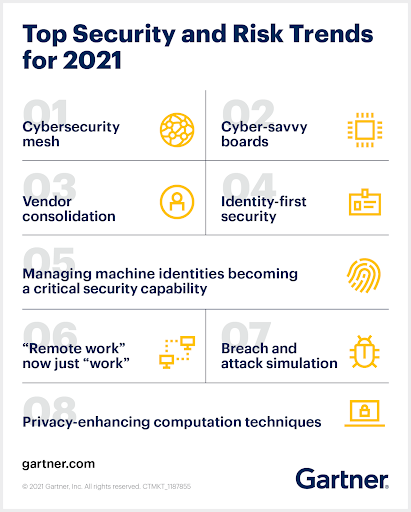
More employees are now working from home or in hybrid arrangements, meaning that there is now a spectrum of vulnerable devices that could serve as an entry point to corporate networks. Therefore, Machine Identity Management has become a vital component of cybersecurity. This rapidly expanding category of online security certifies machines involved in digital connections rather than human actors in general. It is no surprise that Gartner recently named Machine Identity one of the top five growing cybersecurity and risk trends of the year.
Why are identifying machines essential?
A machine identity is a unique key that can identify anything from a physical server to a virtual machine, a Docker container, an IoT device, or any other physical or virtual device or service. Machine identities are used within a data centre to secure communications between microservices, securely connect workloads to services, or facilitate automation processes. Each machine has its own unique identity via its key or certificate, which frequently changes to enhance security. These identities often get shared across devices and flow through different systems before reaching their final destination. This poses significant security risks and makes it hard to have trust, visibility, and control across the security architecture.
For example, a seemingly simple transaction such as connecting with your local bank’s server to check your balance involves interconnecting hundreds of machines, which must be authenticated before connecting. Every one of these connections requires instantaneous authorisation, and if machines cannot correctly identify another device, it becomes challenging to decide whether to allow or deny a connection within them. Another big challenge is ensuring that another party has not intercepted the relayed data. As a result, companies need more resources to manage the same number of machine identities.
For many enterprises, the need is compounded by digital transformation initiatives such as cloud migration and expanding DevOps processes. But when organisations fail to keep up with the volume and variety of machine identities they need, the consequences can be dire. Improper management can lead to devastating cyberattacks, wiping out entire sections of the enterprise’s IT environment all at once. Even companies like Microsoft and Spotify have experienced machine identity outages, resulting in problems ranging from lost customers to compromised security.
Prevention for evolving concerns
Attackers are getting better at compromising these identities and bypassing authentication mechanisms in trusted devices, even though fake digital certificates, giving them a foothold to move to a company’s internal network laterally. According to a study by research firm Vanson Bourne and cybersecurity vendor AppViewX, 61 per cent of enterprises lack core knowledge of their certificates and keys, making them not well equipped to manage machine identities as required. Due to this security gap, 55 per cent of the enterprises reported cybersecurity breaches, and 35 per cent said they experienced organisation-wide system outages. According to Gartner, by 2023, 75 per cent of cloud security failures will result from inadequate management of identities, access, and privileges, up from 50% in 2020.
“Spending on digital transformation projects has skyrocketed in recent years to meet the demands of changed customer and workforce requirements. The combination of an expanding attack surface, rising numbers of identities, and behind-the-curve investment in cybersecurity – what we call Cybersecurity Debt – is exposing organisations to even greater risk, which is already elevated by ransomware threats and vulnerabilities across the software supply chain. This threat environment requires a security-first approach to protecting identities, capable of outpacing attacker innovation,” says Udi Mokady, Founder, Chairman and CEO, CyberArk.
Manual oversight is no longer an option, and digital identities must be managed using device identity management solutions that enable automated provisioning, updates, and de-provisioning of devices throughout their lifecycle. Research shows that automation will be the key, allowing organisations to scale as new technologies are deployed. It is time for data centres to figure out the charge for machine identities. When an enterprise device is not given any special trust status on the network, it must have a way to identify and authorise interactions with other devices, services, or data.
A centralised machine identity management system can address many security concerns, allowing for the automated management of large numbers of certificates. However, there’s also a risk of too much centralisation, creating a single point of failure. Hence critical systems should be truly segmented with a firewall and structured to use their authentication and key management. Establishing a core and cross-functional group with specific responsibility for managing all machine identities is an essential need. The acceleration in digital transformation now means broader adoption of machine identity management, which can prove critical to the future of digital business.
If you liked reading this, you might like our other stories
Datatechvibe Celebrates Cybersecurity Week
When It Comes To Cyber Threats, All Roads Lead To Identity









